For any web browser, the speed and security when surfing the Internet is essential. A quick loading pages allows the user experience improves substantially, this speed has a direct influence on the choice of web browser. Edge Microsoft has incorporated some technologies to enable greater speed and security that we tell you then.
Microsoft Edge and supports TCP Fast Open, but not yet officially for everyone as it is found only in Windows versions Insider Preview. If the EdgeHTML 14.14361 and higher versions enter “about: flags”, we see that we are able to activate the TCP Fast Open will provide us with greater speed when loading web pages.
The road to TLS 1.3
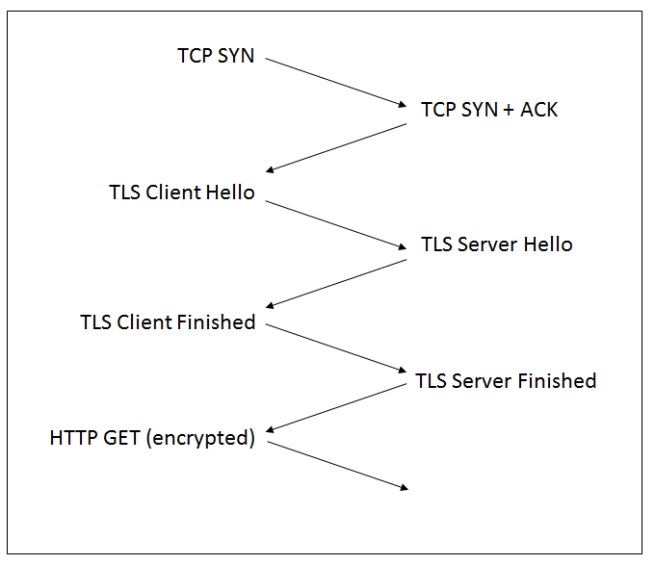
The latest version of the TLS protocol is 1.3, this protocol allows encrypted point to point, today more than half of web connections use TLS to secure web traffic to the user and vice versa, but this number is day increases after day. The current encryption is very fast, many times we have heard myths that said that encryption is slow and therefore is not recommended for use on our website. However, having encryption requires that suites encrypted and the keys are negotiated to establish the connection before you start to download information from the web. Each of these requests is between the client and server is known as RTT (Round Trip Time), and is critical to have the lowest number of RTT.
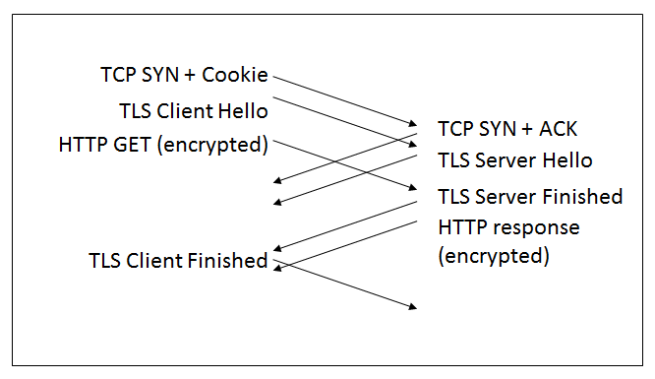
Currently any TLS connection over TCP requires 3 connections RTT to negotiate a RTT for TCP protocol itself and 2 RTT for TLS, this makes the first request to a website with HTTPS later than the rest.
Thanks to TLS 1.3 and use TCP Fast Open and TLS Phase Start, the 3 RTT have been reduced to 1 RTT, allowing the loading time of the page is much smaller, and therefore, the user experience is better .
In the next picture you can see the 3 TCP RTT used in conjunction with the current standard TLS:
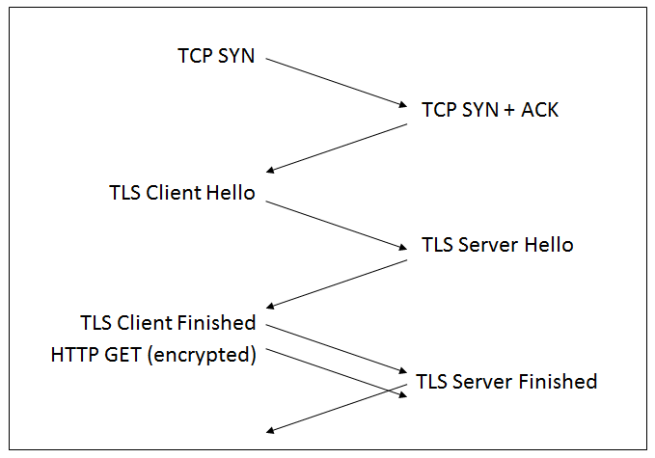
The first improvement: Fast Start TLS
The first improvement that has been made is called TLS Fast Start, this feature allows the client to start sending encrypted data immediately after the first TLS Roundtrip, in this way, we have reduced 2 RTT TLS previously had a 1 RTT only ( must be added in this case 1 more RTT TCP protocol). Microsoft Edge already has enabled this feature with a set of encrypted insurance suites.
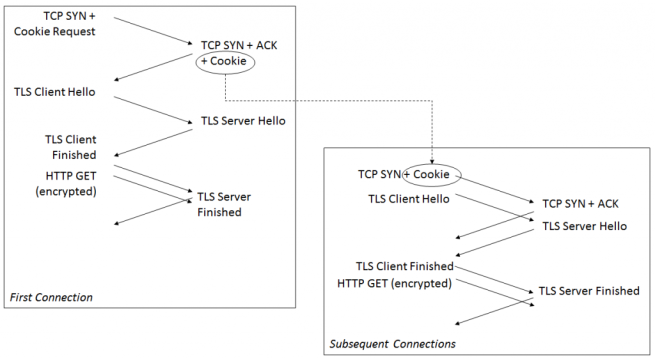
The second improvement: TCP Fast Open
The second improvement has been incorporated to speed up Web browsing is TCP Fast Open this protocol defined in RFC 7413 allows a TCP connection enter a “Fast Open Cookie”. Thanks to this feature, when a client first connects to the server, a cookie is incorporated into the first message TCP SYN, all connections are made and then use the same cookie to begin sending data immediately, before the connection is completed, rather accelerating the process.
If the web server supports TLS Fast Start, the key negotiation can be incorporated simultaneously in the TCP handshake, allowing only have one-RTT before HTTPS traffic begins.
The aim will be 0-RTT with TLS 1.3
The objective pursued is to take 1-RTT 0-RTT to use TLS 1.3, this can do it if we send encryption keys and encrypted data from the client to the server without waiting any previous answer from the server . Thus, the exchange of messages with corresponding wait is minimized.
It is important to mention the issue of security in this part, is that if we network a malicious user could be passed by us capturing and playing back messages. The group of the IETF is working on the security aspect of this scheme provide for cyber criminals do not take advantage of these improvements.
We hope we can soon see these new schemes for HTTPS connection and thus web browsing throttle.
Fuente:https://www.redeszone.net/

Entusiasta de la seguridad cibernética. Especialista en seguridad de la información, actualmente trabajando como especialista en infraestructura de riesgos e investigador.
Experiencia en procesos de riesgo y control, soporte de auditoría de seguridad, diseño y soporte de COB (continuidad del negocio), gestión de grupos de trabajo y estándares de seguridad de la información.
Envía tips de noticias a info@noticiasseguridad.com o www.instagram.com/iicsorg/.
También puedes encontrarnos en Telegram www.t.me/noticiasciberseguridad