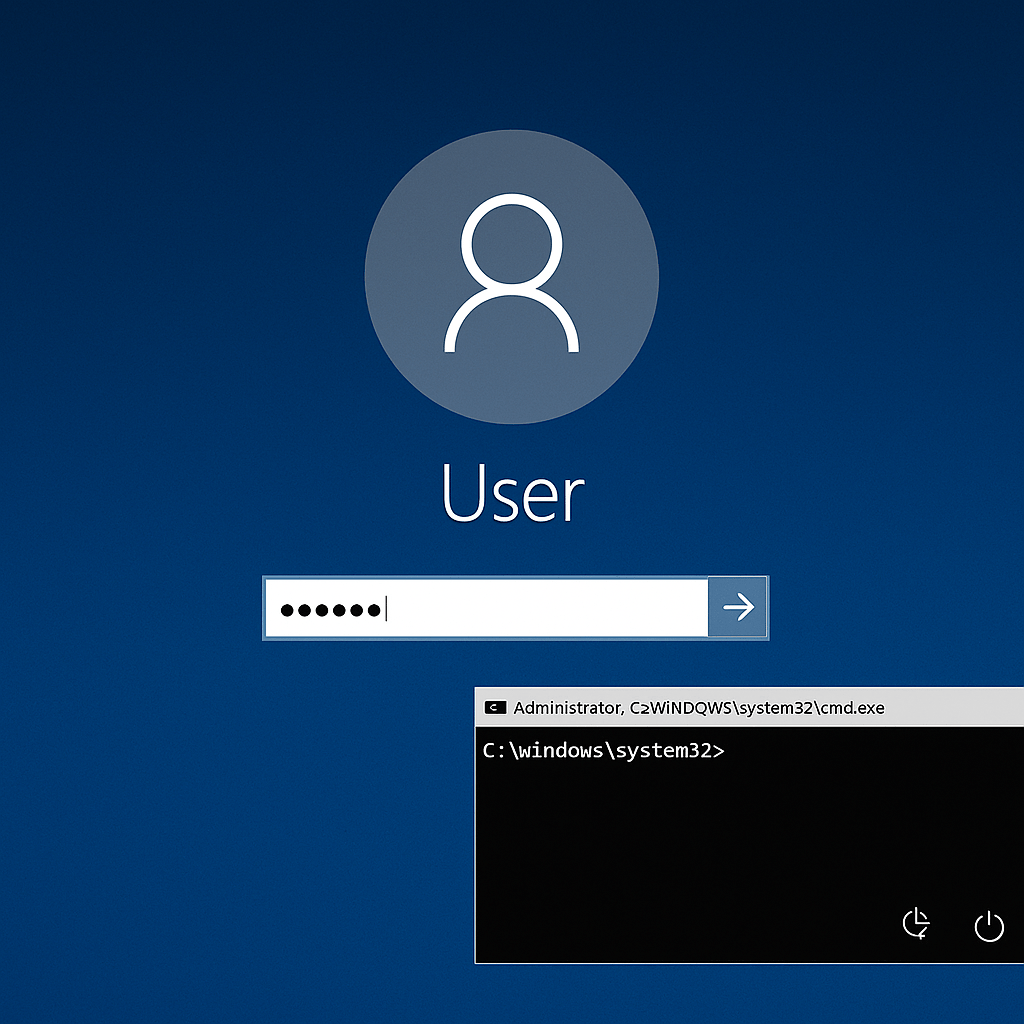
APT3, a group believed to be behind “Operation Clandestine Fox,” is now using exploits targeting recently disclosed vulnerabilities in Windows, researchers at FireEye found.
One of the bugs, CVE-2014-6332, was fixed this Patch Tuesday and noted for being remotely exploitable for 18 years prior to the update. The Windows OLE Automation Array Remote Code Execution vulnerability presented a serious security issue to users, researchers warned, as it impacts every version of Microsoft Windows since Windows 95.
At the time, IBM X-Force Research manager Robert Freeman said that remote exploitation became possible with the release of Internet Explorer 3.0 in 1996, since Visual Basic Script (VBScript) was introduced. In an interview with SCMagazine.com, Freeman explained that exploitation of the bug would be a “tricky” feat, but also “very formulaic” to recreate once saboteurs came up with attack scenarios.
“The same VBScript code will cause the same outcome all of the time,” Freeman said in the interview.
Source:https://www.scmagazine.com/one-bug-had-been-explotiable-for-18-years-prior-to-an-update/article/385073/

Trabajando como arquitecto de soluciones de ciberseguridad, Alisa se enfoca en la protección de datos y la seguridad de datos empresariales. Antes de unirse a nosotros, ocupó varios puestos de investigador de ciberseguridad dentro de una variedad de empresas de seguridad cibernética. También tiene experiencia en diferentes industrias como finanzas, salud médica y reconocimiento facial.
Envía tips de noticias a info@noticiasseguridad.com o www.instagram.com/iicsorg/
También puedes encontrarnos en Telegram www.t.me/noticiasciberseguridad