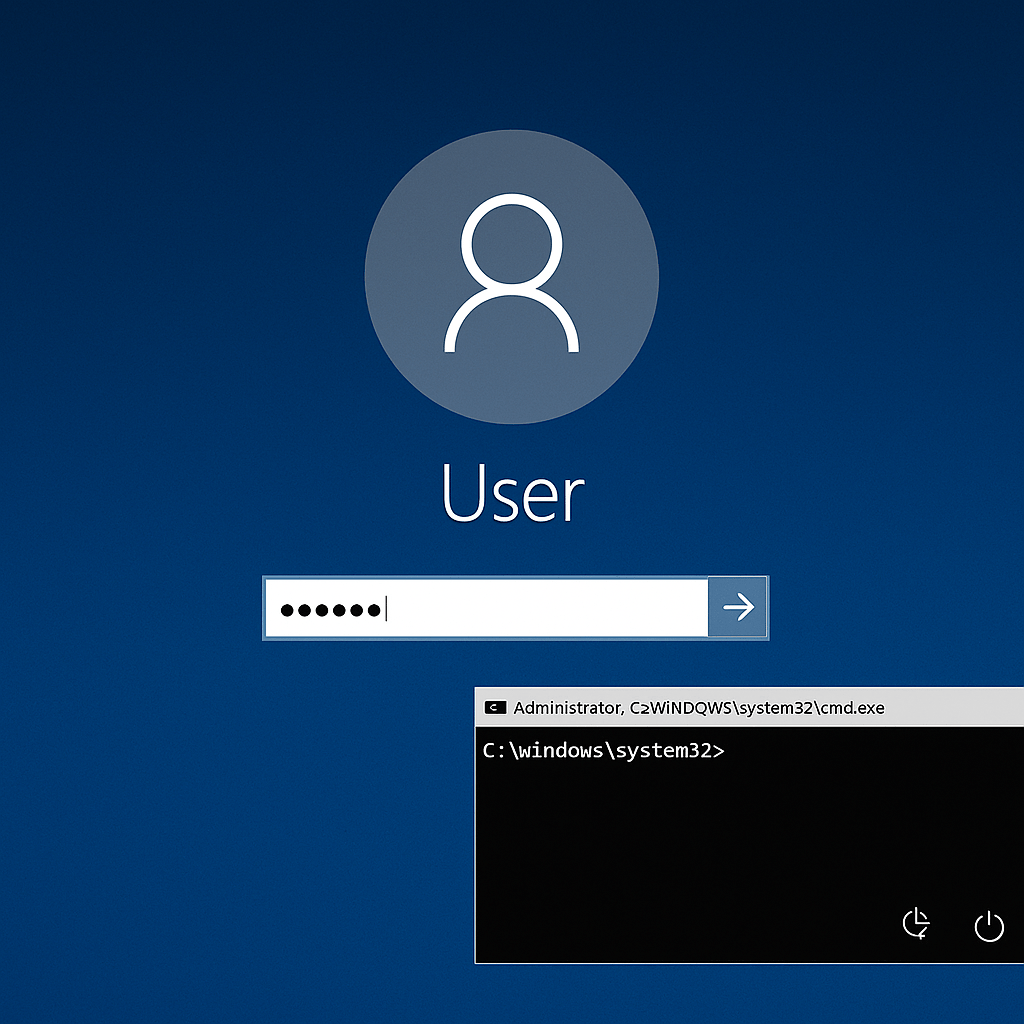
BlackEnergy was first identified several years ago. Initially, BlackEnergy’s custom plugins were used for launching distributed denial-of-service attacks (DDoS). As time went on however, Kaspersky Lab researchers noted, BlackEnergy2 was seen downloading custom spam and banking information-stealer plugins. Eventually, the malware was adopted by the Sandworm team, which has been linked to cyber-espionage.

“The BlackEnergy malware is crimeware turned APT tool and is used in significant geopolitical operations lightly documented over the past year,” Kaspersky Lab researchers blogged Kurt Baumgartner and Maria Garnaeva. “An even more interesting part of the BlackEnergy story is the relatively unknown custom plugin capabilities to attack ARM and MIPS platforms, scripts for Cisco network devices, destructive plugins, a certificate stealer and more.”
Source:https://www.securityweek.com/researchers-go-inside-blackenergy-malware

Trabajando como arquitecto de soluciones de ciberseguridad, Alisa se enfoca en la protección de datos y la seguridad de datos empresariales. Antes de unirse a nosotros, ocupó varios puestos de investigador de ciberseguridad dentro de una variedad de empresas de seguridad cibernética. También tiene experiencia en diferentes industrias como finanzas, salud médica y reconocimiento facial.
Envía tips de noticias a info@noticiasseguridad.com o www.instagram.com/iicsorg/
También puedes encontrarnos en Telegram www.t.me/noticiasciberseguridad